Technology
How to tell if your online accounts have been hacked
More and more hackers are targeting regular individuals with the goal of stealing their crypto, perhaps moving into their bank accounts, or just stalking them. These varieties of attacks are still relatively rare, so there’s no need for alarm. But it’s vital to know what you possibly can do to protect yourself if you watched someone got into your email or social media account.
A number of years ago, I wrote a guide to help people protect themselves, and understand that almost all of the businesses you have an account with already give you tools to take control of your accounts’ security, even before you contact them for help, which in some cases you continue to should do.
Here we break down what you possibly can do on several different online services.
Just like within the previous guide, there’s a vital caveat. You should know that these methods don’t guarantee that you simply haven’t been compromised. If you continue to aren’t sure, you need to contact knowledgeable, especially if you’re a journalist, a dissident or activist, or otherwise someone who has the next risk of being targeted. In those cases, the non-profit Access Now has a digital security helpline that can connect you to one in all their experts.
Another caveat, if you don’t do that already, you need to enable multi-factor authentication on all your accounts, or at the least a very powerful ones (email, banking, social media). This directory is an important resource that teaches you the way to enable multi-factor authentication on greater than 1,000 web sites. (Note that you simply don’t have to use the multi-factor app promoted on that site, there are plenty of other alternatives.)
Increasingly some online services offer using a physical security key or a passkey stored in your password manager, which is one in all the best safeguards to prevent account intrusions that depend on password-stealing malware or phishing.
Gmail lists all of the places your account is energetic
The very first thing you need to do if you watched someone has broken into your Gmail account (and by extension all the opposite Google services linked to it) is to scroll all the best way down in your inbox until you see “Last account activity” in the underside right corner.
Click on “Details.” You will then see a pop-up window that appears like this:
These are all of the places where your Google account is energetic. If you don’t recognize one in all them, for instance if it comes from a distinct location, like a rustic you haven’t visited recently or never been, then click on “Security Checkup.” Here you possibly can see what devices your Google account is energetic in.
If you scroll down, you too can see “Recent security activity.”
Check this list to see if there are any devices that you simply don’t recognize. If in any of those places above you see something suspicious, click on “See unfamiliar activity?” and alter your password:
After you modify your password, as Google explains here, you will probably be signed out of each device in every location, except on the “devices you use to verify that it’s you when you sign in,” and a few devices with third-party apps that you simply’ve granted account access to. If you would like to sign on the market too, go to this Google Support page and click on on the link to “View the apps and services with third-party access.”
Finally, we also suggest considering turning on Google’s Advanced Protection on your account. This enhanced security protection makes phishing your password and hacking into your Google account even harder. The drawback is that you simply need to purchase security keys, hardware devices that function a second-factor. But we expect this method is vital and a must-use for people who find themselves at the next risk.
Also, do not forget that your email account is probably going linked to all your other vital accounts, so moving into it could end up to be step one into hacking into other accounts. That’s why securing your email account is more vital than virtually some other account.
Outlook and Microsoft logins are within the account settings
If you’re concerned about hackers having accessed your Microsoft Outlook account, you possibly can check “when and where you’ve signed in,” as Microsoft puts it within the account settings.
To go to that page, go to your Microsoft Account, click on Security on the left-hand menu, after which under “Sign-in activity” go to “View my activity.”
At this point, you need to see a page that shows recent logins, what platform and device was used to log in, the variety of browser, and the IP address.
If something looks off, click on “Learn how to make your account more secure,” where you possibly can change your password, check “how to get better a hacked or compromised account“, and more.
Microsoft also has a support portal with information on the Recent activity page.
As we noted above, your email account is the cornerstone of your online security, provided that it’s likely that almost all of your vital accounts — think social media, bank, and healthcare provider etc. — are linked to it. It’s a preferred goal for hackers who want to then compromise other accounts.
Like other email providers, Yahoo (which owns TechCrunch) also offers a tool to check your account and sign-in activity with the goal of allowing you to see any unusual activity that could possibly be an indication of compromise.
To access this tool, go to your Yahoo My Account Overview or click on the icon with your initial next to the e-mail icon on the highest right corner, and click on on “Manage your account.”
Once there, click on “Review recent activity.” On this page you’ll give you the option to see recent activity on your account, including password changes, phone numbers added, and what devices are connected to your account, and their corresponding IP addresses.
Given that it is probably going that you simply have linked your email address to sensitive web sites like your bank’s, your social media accounts, and healthcare portals, amongst others, you need to make an additional effort to secure it.
Ensure your Apple ID is secure
Apple allows you to check what devices your Apple ID is logged in directly through the iPhone and Mac system settings, as the corporate explains here.
On an iPhone or iPad, go to “Settings,” tap your name, and scroll down to see all of the devices that you simply are signed in on.
On a Mac, click on the Apple logo on the highest left corner, then “System Settings,” then click on your name, and also you may even see an inventory of devices, similar to on an iPhone or iPad.
If you click on any device, Apple says, you’ll give you the option to “view that device’s information, such as the device model, serial number,” and operating system version.
On Windows, you should use Apple’s iCloud app to check what devices are logged into your account. Open the app, and click on on “Manage Apple ID.” There you possibly can view the devices and get more information on them.
Finally, you too can get this information through the net, going to your Apple ID account page, then clicking on “Devices” within the left hand menu.
How to check Facebook and Instagram security
The social networking giant offers a feature that allows you to see where your account is logged in. Head to Facebook’s “Password and Security” settings and click on on “Where you’re logged in.”

In the identical interface you too can see where you’re logged in with your Instagram account, provided it’s linked to your Facebook account. If the accounts should not linked, or you simply don’t have a Facebook account, go to Instagram’s “Account Center” to manage your Instagram account and click on on Password and Security, after which “Where you’re logged in.”
Here you possibly can select to sign off from specific devices, perhaps since you don’t recognize them, or because they’re old devices you don’t use anymore.
Just like Google, Facebook offers an Advanced Protection feature in addition to for Instagram, which essentially makes it harder for malicious hackers to log onto your account. “We’ll apply stricter rules at login to reduce the chances of unauthorized access to your account,” the corporate explains. “If we see anything unusual about a login to your account, we’ll ask you to complete extra steps to confirm it’s really you.”
If you’re a journalist, a politician, or otherwise someone who’s more likely in danger to be targeted by hackers, you could want to activate this feature.
It’s easy to see whether your WhatsApp is secure
In the past, it was only possible to use WhatsApp on one mobile device only. Now, Meta has added functionalities for WhatsApp users to use the app on computers, and likewise directly via browser.
Checking where you logged in with your WhatsApp account is easy. Open the WhatsApp app on your cell phone. On iPhones and iPads, tap on the Settings icon in the underside right corner, then tap on “Linked devices.”
There, you’ll give you the option to see an inventory of devices, and by clicking on one in all them you possibly can log them out.
On Android, tap on the three dots in the highest right corner of the WhatsApp app, then tap “Linked devices” and you will notice a page that’s very similar to what you’d see on Apple devices.
Signal also allows you to check for anomalies
Like WhatsApp, Signal now allows you to use the app via dedicated Desktop apps for macOS, Windows, in addition to Linux.
From this screen of Linked Devices, you possibly can tap on “Edit” and take away the devices, which implies your account will probably be logged out and unlinked from those devices.
X (Twitter) allows you to see what sessions are open
To see where you’re logged into X (formerly Twitter), go to X Settings, then click on “More” on the left hand menu, click on “Settings and privacy,” then “Security and account access,” and eventually “Apps and sessions.”
From this menu, you possibly can see what apps you have connected to your X account, what sessions are open (equivalent to where you’re logged in), and the access history of your account.
You can revoke access to all other devices and locations by hitting the “Log out of all other sessions” button.
Technology
Trump to sign a criminalizing account of porn revenge and clear deep cabinets

President Donald Trump is predicted to sign the act on Take It Down, a bilateral law that introduces more severe punishments for distributing clear images, including deep wardrobes and pornography of revenge.
The Act criminalizes the publication of such photos, regardless of whether or not they are authentic or generated AI. Whoever publishes photos or videos can face penalty, including a advantageous, deprivation of liberty and restitution.
According to the brand new law, media firms and web platforms must remove such materials inside 48 hours of termination of the victim. Platforms must also take steps to remove the duplicate content.
Many states have already banned clear sexual desems and pornography of revenge, but for the primary time federal regulatory authorities will enter to impose restrictions on web firms.
The first lady Melania Trump lobbyed for the law, which was sponsored by the senators Ted Cruz (R-TEXAS) and Amy Klobuchar (d-minn.). Cruz said he inspired him to act after hearing that Snapchat for nearly a 12 months refused to remove a deep displacement of a 14-year-old girl.
Proponents of freedom of speech and a group of digital rights aroused concerns, saying that the law is Too wide And it will probably lead to censorship of legal photos, similar to legal pornography, in addition to government critics.
(Tagstransate) AI
Technology
Microsoft Nadella sata chooses chatbots on the podcasts

While the general director of Microsoft, Satya Nadella, says that he likes podcasts, perhaps he didn’t take heed to them anymore.
That the treat is approaching at the end longer profile Bloomberg NadellaFocusing on the strategy of artificial intelligence Microsoft and its complicated relations with Opeli. To illustrate how much she uses Copilot’s AI assistant in her day by day life, Nadella said that as a substitute of listening to podcasts, she now sends transcription to Copilot, after which talks to Copilot with the content when driving to the office.
In addition, Nadella – who jokingly described her work as a “E -Mail driver” – said that it consists of a minimum of 10 custom agents developed in Copilot Studio to sum up E -Mailes and news, preparing for meetings and performing other tasks in the office.
It seems that AI is already transforming Microsoft in a more significant way, and programmers supposedly the most difficult hit in the company’s last dismissals, shortly after Nadella stated that the 30% of the company’s code was written by AI.
(Tagstotransate) microsoft
Technology
The planned Openai data center in Abu Dhabi would be greater than Monaco

Opeli is able to help in developing a surprising campus of the 5-gigawatt data center in Abu Dhabi, positioning the corporate because the fundamental tenant of anchor in what can grow to be considered one of the biggest AI infrastructure projects in the world, in accordance with the brand new Bloomberg report.
Apparently, the thing would include a tremendous 10 square miles and consumed power balancing five nuclear reactors, overshadowing the prevailing AI infrastructure announced by OpenAI or its competitors. (Opeli has not yet asked TechCrunch’s request for comment, but in order to be larger than Monaco in retrospect.)
The ZAA project, developed in cooperation with the G42-Konglomerate with headquarters in Abu Zabi- is an element of the ambitious Stargate OpenAI project, Joint Venture announced in January, where in January could see mass data centers around the globe supplied with the event of AI.
While the primary Stargate campus in the United States – already in Abilene in Texas – is to realize 1.2 gigawatts, this counterpart from the Middle East will be more than 4 times.
The project appears among the many wider AI between the USA and Zea, which were a few years old, and annoyed some legislators.
OpenAI reports from ZAA come from 2023 Partnership With G42, the pursuit of AI adoption in the Middle East. During the conversation earlier in Abu Dhabi, the final director of Opeli, Altman himself, praised Zea, saying: “He spoke about artificial intelligence Because it was cool before. “
As in the case of a big a part of the AI world, these relationships are … complicated. Established in 2018, G42 is chaired by Szejk Tahnoon Bin Zayed Al Nahyan, the national security advisor of ZAA and the younger brother of this country. His embrace by OpenAI raised concerns at the top of 2023 amongst American officials who were afraid that G42 could enable the Chinese government access advanced American technology.
These fears focused on “G42”Active relationships“With Blalisted entities, including Huawei and Beijing Genomics Institute, in addition to those related to people related to Chinese intelligence efforts.
After pressure from American legislators, CEO G42 told Bloomberg At the start of 2024, the corporate modified its strategy, saying: “All our Chinese investments that were previously collected. For this reason, of course, we no longer need any physical presence in China.”
Shortly afterwards, Microsoft – the fundamental shareholder of Opeli together with his own wider interests in the region – announced an investment of $ 1.5 billion in G42, and its president Brad Smith joined the board of G42.
(Tagstransate) Abu dhabi
-

 Press Release1 year ago
Press Release1 year agoU.S.-Africa Chamber of Commerce Appoints Robert Alexander of 360WiseMedia as Board Director
-
 Press Release1 year ago
Press Release1 year agoCEO of 360WiSE Launches Mentorship Program in Overtown Miami FL
-

 Business and Finance12 months ago
Business and Finance12 months agoThe Importance of Owning Your Distribution Media Platform
-

 Business and Finance1 year ago
Business and Finance1 year ago360Wise Media and McDonald’s NY Tri-State Owner Operators Celebrate Success of “Faces of Black History” Campaign with Over 2 Million Event Visits
-

 Ben Crump1 year ago
Ben Crump1 year agoAnother lawsuit accuses Google of bias against Black minority employees
-
 Theater1 year ago
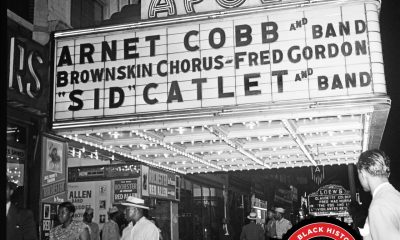
Theater1 year agoTelling the story of the Apollo Theater
-

 Ben Crump1 year ago
Ben Crump1 year agoHenrietta Lacks’ family members reach an agreement after her cells undergo advanced medical tests
-

 Ben Crump1 year ago
Ben Crump1 year agoThe families of George Floyd and Daunte Wright hold an emotional press conference in Minneapolis
-

 Theater1 year ago
Theater1 year agoApplications open for the 2020-2021 Soul Producing National Black Theater residency – Black Theater Matters
-
 Theater12 months ago
Theater12 months agoCultural icon Apollo Theater sets new goals on the occasion of its 85th anniversary























